BOSTON, MASS. and TEL AVIV, ISRAEL, November 28, 2023 - A severe design flaw in Google Workspace's domain-wide delegation feature discovered by threat hunting experts from Hunters’ Team Axon, can allow attackers to misuse existing delegations, enabling privilege escalation and unauthorized access to Workspace APIs without Super Admin privileges. Such exploitation could result in theft of emails from Gmail, data exfiltration from Google Drive, or other unauthorized actions within Google Workspace APIs on all of the identities in the target domain. Hunters has responsibly disclosed this to Google and worked closely with them prior to publishing this research.
Domain-wide delegation permits a comprehensive delegation between Google Cloud Platform (GCP) identity objects and Google Workspace applications. In other words, it enables GCP identities to execute tasks on Google SaaS applications, such as Gmail, Google Calendar, Google Drive, and more, on behalf of other Workspace users.
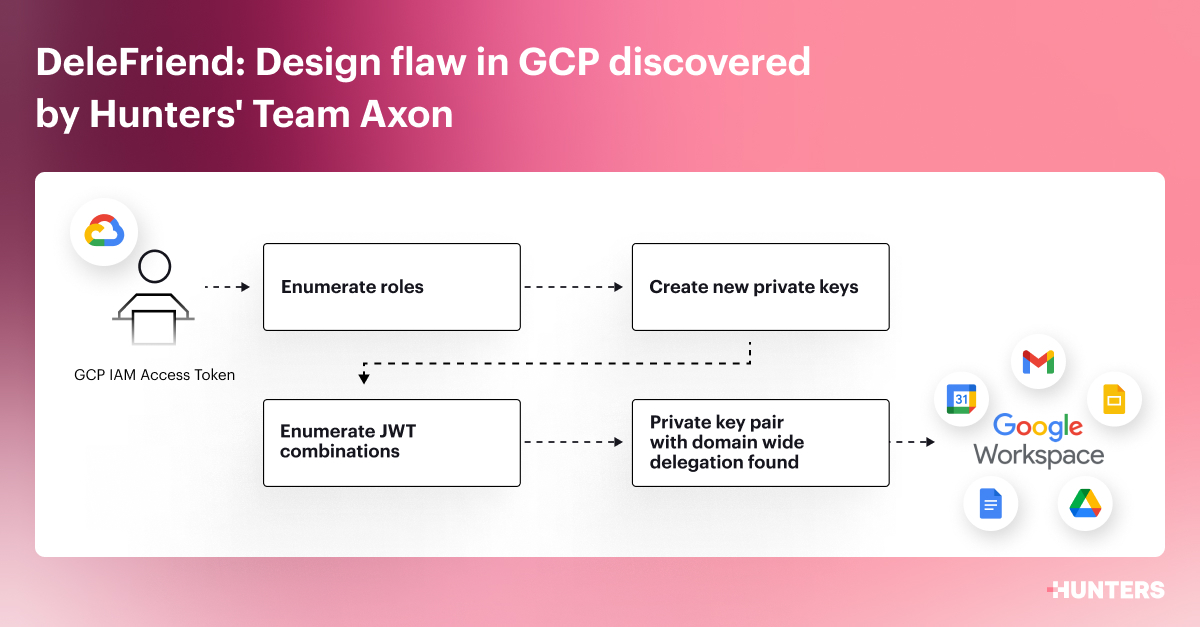
The design flaw, which the team at Hunters has dubbed “DeleFriend,” allows potential attackers to manipulate existing delegations in GCP and Google Workspace without possessing the high-privilege Super Admin role on Workspace, which is essential for creating new delegations. Instead, with less privileged access to a target GCP project, they can create numerous JSON web tokens (JWTs) composed of different OAuth scopes, aiming to pinpoint successful combinations of private key pairs and authorized OAuth scopes which indicate that the service account has domain-wide delegation enabled.
The root cause lies in the fact that the domain delegation configuration is determined by the service account resource identifier (OAuth ID), and not the specific private keys associated with the service account identity object.
Additionally, no restrictions for fuzzing of JWT combinations were implemented on the API level, which does not restrict the option of enumerating numerous options for finding and taking over existing delegations.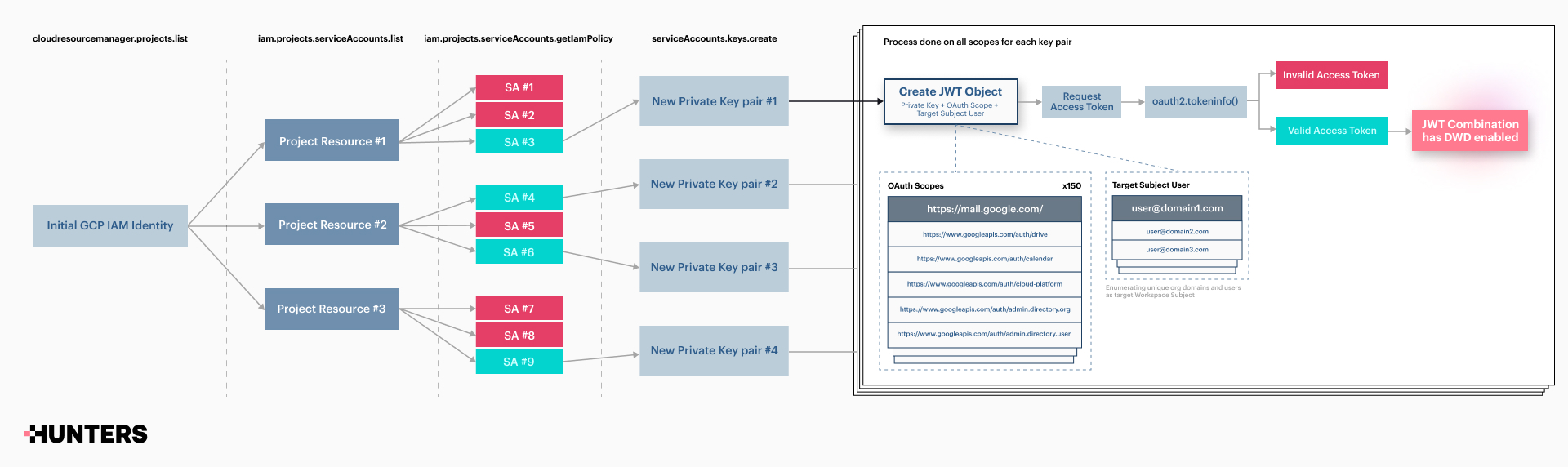
This flaw poses a special risk due to potential impact described above and is amplified by the following:
- Long Life: By default, GCP Service account keys are created without an expiry date. This feature makes them ideal for establishing backdoors and ensuring long-term persistence.
- Easy to hide: The creation of new service account keys for existing IAMs or, alternatively, the setting of a delegation rule within the API authorization page is easy to conceal. This is because these pages typically host a wide array of legitimate entries, which are not examined thoroughly enough.
- Awareness: IT and Security departments may not always be cognizant of the domain-wide delegation feature. They might especially be unaware of its potential for malicious abuse.
- Hard to detect: Since delegated API calls are created on behalf of the target identity, the API calls will be logged with the victim details in the corresponding GWS audit logs. This makes it challenging to identify such activities.
“The potential consequences of malicious actors misusing domain-wide delegation are severe. Instead of affecting just a single identity, as with individual OAuth consent, exploiting DWD with existing delegation can impact every identity within the Workspace domain,” says Yonatan Khanashvili of Hunters’ Team Axon.
The range of possible actions varies based on the OAuth scopes of the delegation. For instance, email theft from Gmail, data exfiltration from the drive, or monitor meetings from Google Calendar.
In order to execute the attack method, a particular GCP permission is needed on the target Service Accounts. However, Hunters observed that such permission is not an uncommon practice in organizations making this attack technique highly prevalent in organizations that don’t maintain a security posture in their GCP resources. “By adhering to best practices, and managing permissions and resources smartly, organizations can dramatically minimize the impact of the attack method” Khanashvili continued.
Hunters has created a proof-of-concept tool (full details are included in the full research) to assist organizations in detecting DWD misconfigurations, increasing awareness, and reducing DeleFriend’s exploitation risks. Using this tool, red teams, pen testers, and security researchers can simulate attacks and locate vulnerable attack paths of GCP IAM users to existing delegations in their GCP Projects to evaluate (and then improve) the security risk and posture of their Workspace and GCP environments.
Hunters’ Team Axon has also compiled comprehensive research that lays out exactly how the vulnerability works as well as recommendations for thorough threat hunting, detection techniques, and best practices for countering domain-wide delegation attacks.
Hunters responsibly reported DeleFriend to Google as part of Google’s “Bug Hunters” program in August, and are collaborating closely with Google's security and product teams to explore appropriate mitigation strategies. Currently, Google has yet to resolve the design flaw.
DeleFriend FAQs
What are the prerequisites for an attack?
The necessary prerequisites include having initial access to a GCP IAM user, along with permission to generate private keys for service accounts. This specific permission can be exploited for Domain-Wide delegation abuse, resulting in a complete takeover of the Google Workspace domain. The exploitation could result in theft of emails from Gmail, data exfiltration from Google Drive, or other unauthorized actions within Google Workspace on all of the identities in the target domain.
How easy, or not, is it to abuse it?
DeleFriend’s exploitation method enables the complete control of an entire Workspace domain. Executing this exploit manually is not straightforward, as it involves experimenting with various combinations of "authorization". However, with the POC we have released, this process can be automated, offering a simpler approach.
Important: The DeleFriend POC tool was created as a proof-of-concept tool to increase awareness around OAuth delegation attacks in GCP and Google Workspace and to improve the security posture of organizations that use the Domain-Wide-Delegation feature. DeleFriend POC tool should be used solely for authorized security research purposes. This tool is provided “as is” and Hunters disclaims any and all warranties and liabilities regarding the use/misuse of this tool. Use responsibly.
What ideally would/should have been a better/more secure design?
We have proposed several ideas to enhance Google's design, with the primary suggestion being to modify the delegation configuration to depend on a specific private key, rather than an entire service account. Alternatively, making this an optional requirement could transfer the risk to the user. Additionally, some straightforward fixes include limiting the number of JWT combination requests using the same key in a short time frame, and revising the overly generous permissions associated with the Editor Role.
The report says that a particular GCP permission is required for an attacker to be able to execute Hunter's attack method. Is this a GCP permission with a high-level of privileges?
The necessary GCP permission for targeting service accounts can be assigned in various ways, including custom roles, and most frequently through the "Editor” Role. While this role is deemed to hold high privileges in GCP, it doesn't quite reach the permission level required for creating Domain-Wide Delegation, which is the Super Admin, the highest level of permission within the Workspace domain.
Our research indicates that the use of the permission to create keys on service accounts is widespread in organizations within different roles and its impact is significant. Additionally, the Editor role specifically is notably prevalent in attack scenarios, often being acquired by adversaries at some point during an incident.
What has Google's response been? Is the company doing anything to fix the issue?
The issue was reported to Google in August 2023 and accepted in November 2023. Google is currently reviewing the issue with their Product team to assess potential actions based on our recommendations. Addressing a design flaw is a complex task, as various consequences could impact the functionality. Google was notified prior to our publication, and we believe that raising awareness about this design flaw can assist organizations in reducing risks and detecting potential exploitations.
What can organizations do to mitigate risk?
To mitigate the risks, several measures can be implemented, beginning with the establishment of secure roles and permissions within GCP projects, and the vigilant monitoring for potential exploitation attempts. Our research paper includes a dedicated section detailing how to detect and investigate such issues, along with implementing best practices to minimize the risk of Delefriend exploitation.
About Hunters
Hunters delivers a Security Operations Center (SOC) Platform that reduces risk, complexity, and cost for security teams. A SIEM alternative, Hunters SOC Platform provides data ingestion, built-in and always up-to-date threat detection, and automated correlation and investigation capabilities, minimizing the time to understand and respond to real threats.
Organizations like Booking.com, ChargePoint, Yext, Upwork and Cimpress leverage Hunters SOC Platform to empower their security teams.
Hunters is backed by leading VCs and strategic investors including Stripes, YL Ventures, DTCP, Cisco Investments, Bessemer Venture Partners, U.S. Venture Partners (USVP), Microsoft’s venture fund M12, Blumberg Capital, Snowflake, Databricks, and Okta.
Learn more about Hunters at www.hunters.security.